sudoplz: Approving sudo commands in Claude Code and Cursor
Claude Code and Cursor on Linux can't handle interactive terminal prompts. If you ask the agent to run sudo apt install something and you get sudo: Authentication failed. I want the ability to do case-by-case review and approval of sudo commands, the same as I can already do with any other command.
The common workarounds all have problems. Anthropic's official recommendation is to whitelist specific commands in /etc/sudoers and .claude/settings.json, which requires predicting every command the agent will ever need. Passwordless sudo gives the agent — and anything else running as my user — unrestricted root. Until now, I've been copy-pasting commands, which is unacceptable in the year 2026.
A thread on the Claude Code tracker pointed me at the approach that solves this, and I've packaged it as sudoplz.
How it works
sudo has a built-in hook for non-interactive password entry: SUDO_ASKPASS. Given a program that produces your password on stdout, the sudo -A <cmd> invokes that program instead of prompting for your password interactively in the terminal.
By setting SUDO_ASKPASS to sudoplz, every time the agent runs sudo -A:
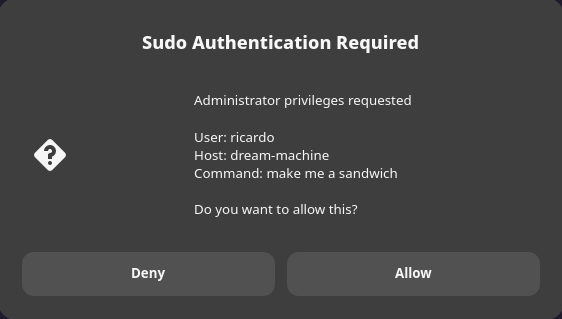
- A dialog pops up showing the exact command about to run
- If you click Allow, it decrypts your sudo password using your SSH private key
- If you click Deny, sudo gets nothing and fails
The password is stored encrypted with age (for Ed25519 keys) or OpenSSL (for RSA). Along with the SSH-key gate, there's a caller-path whitelist, parent-process whitelist, rate limiting, and automatic expiration. The threat model assumes a personal workstation with an encrypted disk and a passphrase-protected SSH key — not a shared or production system.
Using it
uv tool install sudoplz
export SUDO_ASKPASS="$(which askpass)"
sudoplz set # store the password, once
sudo -A systemctl start tailscaled # agents can now do this
Full setup, TOTP fallback for SSH sessions, and security configuration are in the README.
Credits
The idea — an SSH-key-encrypted sudo password served via SUDO_ASKPASS, gated by a confirmation dialog — is from GlassOnTin/secure-askpass. That project is dormant and had a bunch of issues. sudoplz is a substantially rewritten and cleaned up fork.